ServiceNow Workflow Exposure
See the full execution path behind your ServiceNow workflows.
ServiceNow shows the workflow. Entra shows the identity. Neither shows what happens when they interact — what the automation actually reaches, where permissions have drifted, and whether anyone is still accountable.
Start 30-Day EvaluationDashboards look clean. The execution chain underneath may not.
Many enterprises have production ServiceNow workflows that continue to run without clear control visibility — because ownership, permission drift, and external reach sit across multiple systems.
Exposure surface
Script Includes, Flow Designer automations, OAuth credentials, REST message definitions — all tied to identities that reach Microsoft Graph, Azure, and external services.
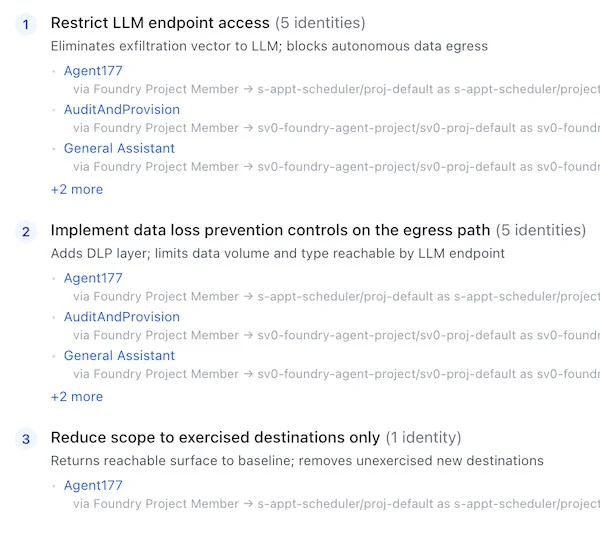
Remediation path
Findings are structured for direct handoff into ServiceNow or JIRA — the same platform where remediation happens.
Common exposure patterns
Structural patterns found in ServiceNow environments — recurring, evidence-based, and tied to specific execution paths.
Active workflows with no accountable owner
A production workflow is active, but no valid accountable owner exists for the workflow or the identity behind it.
Immediate hygiene, control, and approval issue — even without any AI adoption.
Workflow identities with broader access than approved
The workflow appears unchanged, but the identity behind it now has broader permissions, roles, or downstream reach than originally intended. The process runs with more authority than the business expects or approved.
Workflows that reach external or AI-connected services
A workflow handling sensitive processes or data is tied to an identity that can also reach an external service or AI endpoint. Concrete review and containment issue.
What the platform surfaces
- Full authority path from ServiceNow workflow to downstream system to data domain
- Scope drift — where integration accounts have gained permissions beyond original intent
- Ownership status for every workflow identity in scope
- External egress — which workflow paths reach services outside the intended boundary
- Data domain sensitivity — what classification of data the workflow path can reach
Findings your team can act on immediately.
Prioritized by real impact
Every finding tied to a specific workflow, identity, and execution path — with the evidence to prove it
Remediation guidance included
Structural actions that reduce exposure without disrupting running processes
Workflow-ready format
Structured for direct handoff into ServiceNow, JIRA, or your existing remediation process
Executive-ready evidence
One-line business risk statements. Audit-grade documentation for leadership and compliance
This is relevant if…
- Production ServiceNow workflows connect to Microsoft Graph or external APIs and the full path hasn't been reviewed
- Integration accounts have been active for over a year with no scope or ownership check
- You need audit-ready evidence of which workflows can reach sensitive data
Audit your ServiceNow workflow exposure.
See the full execution path behind your workflows.
Start 30-Day Evaluation