Automation & NHI Exposure
See what your automation identities can actually reach across Entra and Azure.
Entra shows identities. Azure shows role assignments. Neither shows the full execution path — what automations actually reach across systems, where access has exceeded intent, and where ownership no longer holds up.
Start 30-Day EvaluationEach system looks governed. The execution chain tells a different story.
Entra shows the identity. Azure shows the role assignment. But when a service principal runs an automated workflow that reaches Microsoft Graph, sensitive data domains, or an external AI endpoint — that full path isn't visible in any single tool.
Environments can appear governed locally while material execution risk builds underneath.
Common exposure patterns
Structural patterns found in production environments — recurring, evidence-based, and tied to specific execution paths.
Active automations with no valid owner
A service principal, managed identity, or automation remains active in production without a valid accountable owner.
Service principal owner departed. Runtime identity: not assigned.
Service principals with more permissions than approved
The process still runs, but the service principal or managed identity behind it now has broader Entra roles, Azure permissions, or downstream reach than originally intended.
Automations that can reach AI services or external endpoints
An automation touching sensitive data can also reach AI services, external endpoints, or additional Microsoft services not reviewed as part of the original design.
What the platform surfaces
- The full authority path across Entra, Azure, and Microsoft Graph
- Scope drift since baseline — specific role and permission changes
- Ownership status for every automation identity in scope
- External egress detection — which paths reach services outside the intended boundary
- Data domain sensitivity — what classification of data the automation path can reach
Findings your team can act on immediately.
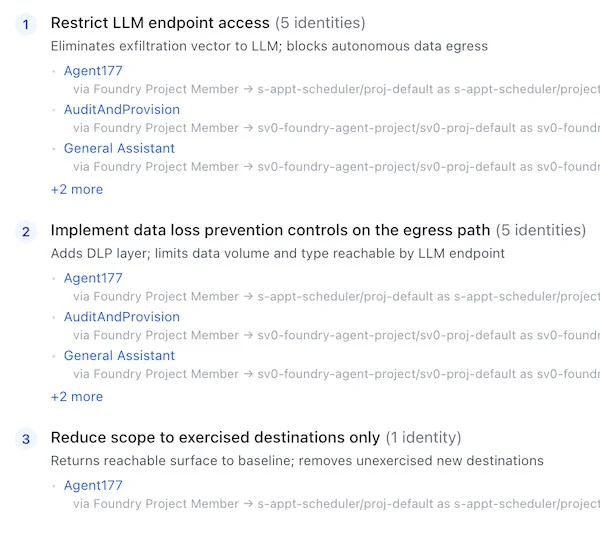
Prioritized by real impact
Every finding tied to a specific automation, identity, and execution path — with the evidence to prove it
Remediation guidance included
Structural actions that reduce exposure without disrupting running processes
Workflow-ready format
Structured for direct handoff into ServiceNow, JIRA, or your existing remediation process
Executive-ready evidence
One-line business risk statements. Audit-grade documentation for leadership and compliance
This is relevant if…
- Service principals or managed identities in Entra ID have not had a documented access review in the past year
- You can't trace what a given automation can reach across Azure and Entra
- AI-connected services are approaching production and you don't have evidence of their access scope
Map your Entra and Azure automation exposure.
See what your automation identities can actually reach.
Start 30-Day Evaluation