Know what your automations can access.
See which automations can reach critical systems, sensitive data, and external services — and where ownership or permissions no longer hold up.
Start 30-Day Evaluation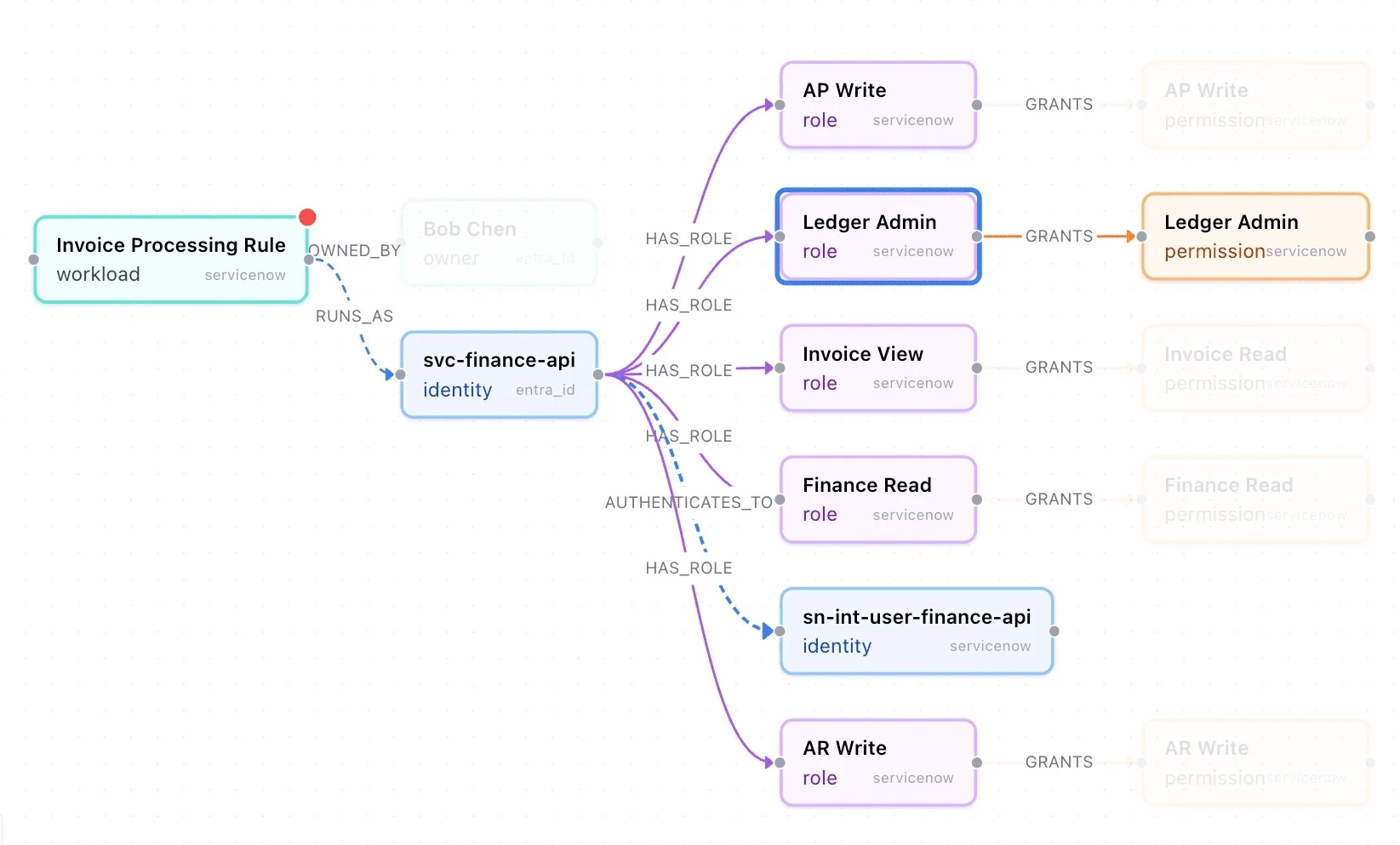
See which automations can reach critical systems, sensitive data, and external services — and where ownership or permissions no longer hold up.
Start 30-Day Evaluation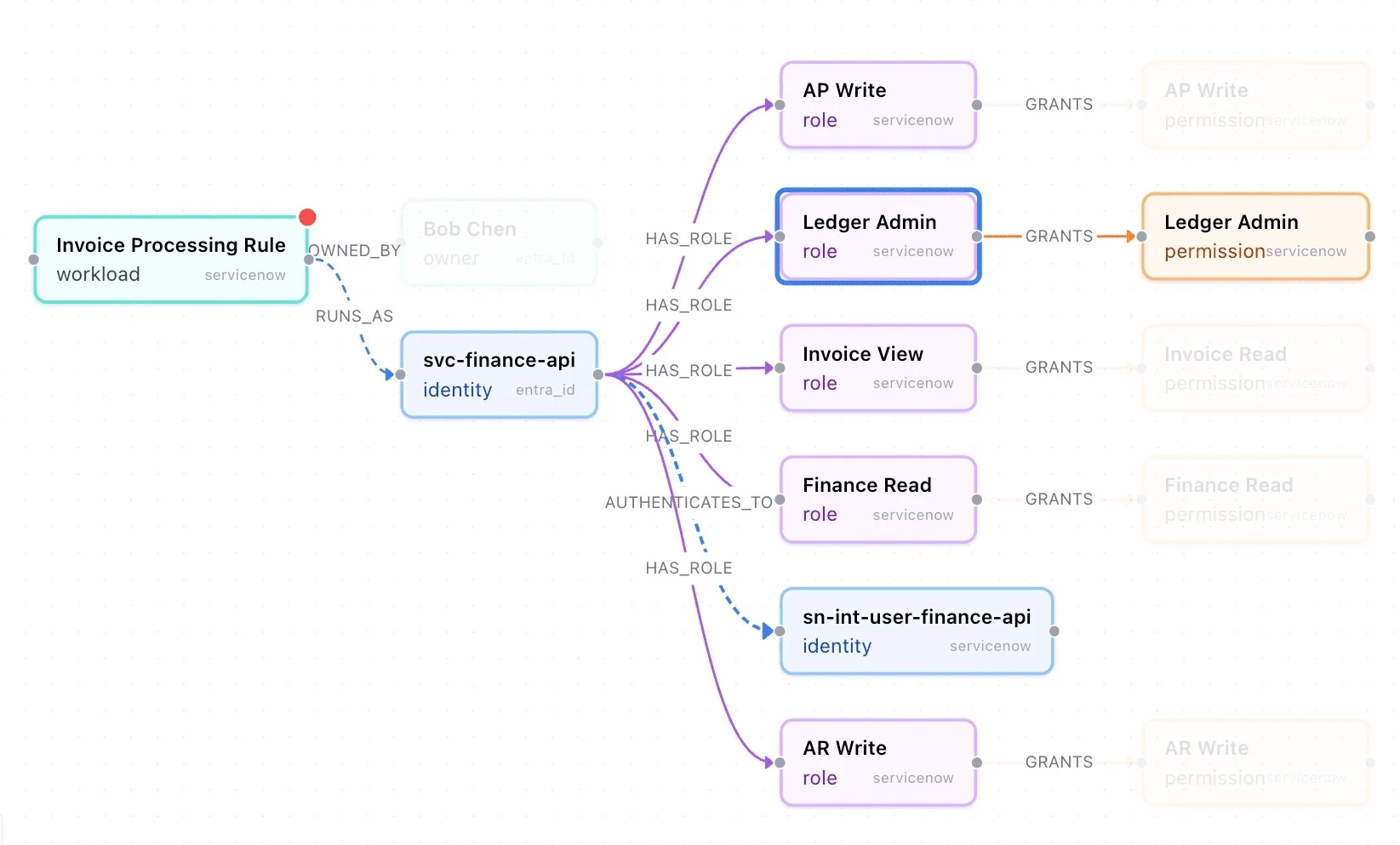
ServiceNow manages the workflow. Entra manages the identity. Azure manages the application. Each system appears correct on its own.
None of them show what happens when those systems interact during execution — what automation actually runs, what it reaches, and what data it can access or expose.
The risk is not in any single system. It appears when systems interact during execution.
Structural exposure across automations and non-human identities — recurring, systemic, and invisible to existing tools.
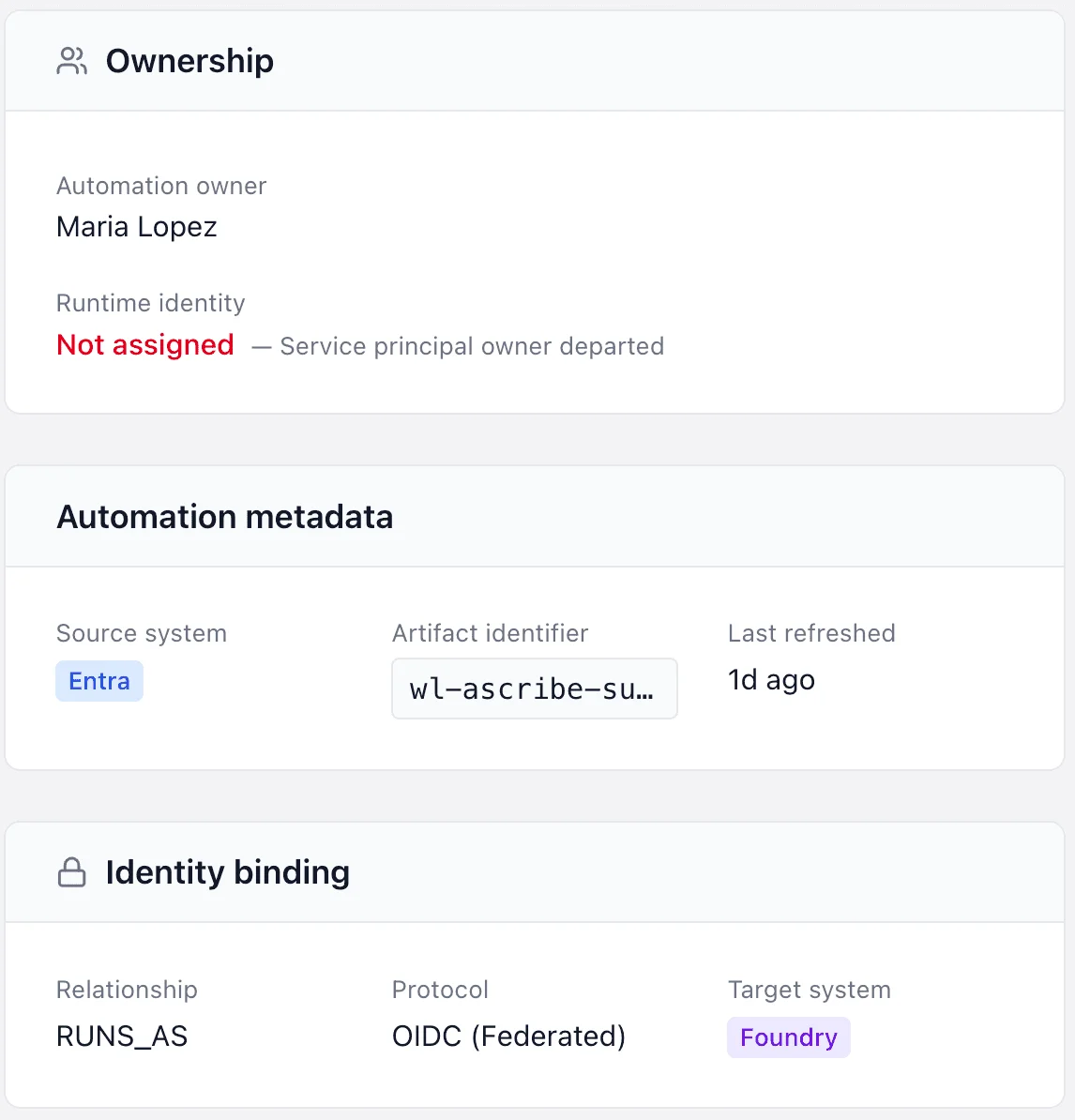
Workflows and service accounts running in production without a valid owner. The identity is active. No one is responsible for it.
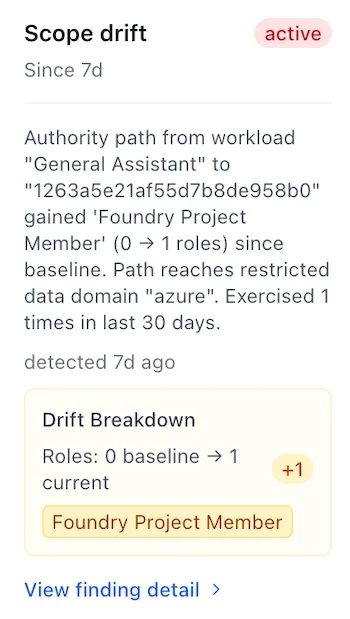
Permissions, roles, or downstream reach have expanded beyond original intent. The process still runs — with more authority than the business approved.
Automations that can send data to external systems — including AI and LLM endpoints — without that path having been reviewed or controlled.
Every pattern is structural, evidence-based, and tied to a specific automation path — not an inferred risk score.
Sensitive data exposure across automation paths
Over-privileged service accounts and hidden access
Access that bypasses expected controls
External egress to AI and LLM endpoints
Automation risk before production deployment
Not alert noise. Not a posture score. Evidence-based findings with remediation guidance your team can act on immediately.
Every finding is tied to a specific workflow and identity — with the full path, scope change, and business risk in one view.
Structural actions that reduce exposure without disrupting running processes. Not just what's wrong — what to change.
Executive-ready risk statements. Audit evidence. Prioritized by real operational impact — not alert volume.
Production automations run across ServiceNow, Entra, or Azure — and no one has mapped what they actually reach
Service accounts have been active for over a year without a documented access review
Automation identities have accumulated permissions beyond their original scope — and no one has re-scoped them
Internal workflows can reach external services or AI endpoints — and that path has never been reviewed
An audit is coming and you need evidence of active governance over non-human identities
Read-only. Metadata-only. No content inspection. 100% deterministic findings. First findings in hours.
Start 30-Day Evaluation